Smartphone Filming as a Data Leak Vector: Real Cases and Prevention
Organizations can deploy DLP, disable USB ports, and monitor every email attachment — and still be vulnerable to a form of data exfiltration that bypasses all of it. An employee raising their smartphone and photographing a monitor screen, sometimes called visual hacking, leaves no digital footprint, produces no network traffic, and triggers no security alerts.
TL;DR
- Smartphone photography of monitor screens leaves no trace in DLP logs or network records, making it undetectable by conventional security tools.
- Real-world insider threat incidents consistently identify smartphone filming as one of the primary methods for extracting sensitive data.
- Preventing smartphone filming requires a combination of physical access controls, clear policy, and AI-based real-time detection.
Why Smartphone Filming Evades Security Detection
One of the scenarios security teams dread most is a quiet, traceless exfiltration — data walking out the door without triggering a single alert. Photographing a monitor with a smartphone fits this description precisely.
Most data exfiltration attempts — file copying, email forwarding, USB connections — generate system logs. DLP solutions monitor these pathways and raise alerts when anomalies appear. But an employee who pulls out their phone and takes a photo of a screen falls entirely outside the detection scope of any software. There is no network traffic, no file system access, and no change to any company-managed device.
This simple fact — that smartphone photography does not use a digital pathway — creates a structural gap in conventional security architecture.
What Has Actually Happened
Visual hacking is not a theoretical threat. Documented cases across industries make clear how frequently this technique appears in real insider threat incidents.
Financial Sector Insider Cases
A notable pattern in financial sector data leak incidents involves employees photographing customer account information, investment portfolios, and loan application data on their screens and transmitting the images through personal channels. Because no digital transfer occurs on company systems, these incidents often take months to surface. When they do, the discovery typically comes not from security logs but from a client complaint, a regulatory inquiry, or a competitor's suspiciously accurate intelligence.
The Financial Supervisory Service's 2023 Information Security Survey noted that insider threats consistently account for a significant share of actual data leaks at financial firms, with physical media and physical access methods remaining prominent vectors.
R&D Trade Secret Exfiltration
In manufacturing and technology companies, a recurring pattern involves employees in the weeks before departure photographing screens displaying proprietary technical documentation. Because they access the information through their normal job functions and transfer nothing digitally, DLP systems detect no unusual activity. The exfiltration is only discovered after the employee joins a competitor and that competitor's product reveals detailed knowledge of the source company's internal designs.
The Ponemon Institute's 2024 Cost of Insider Risks Global Report placed the average cost of a malicious insider incident at over $700,000, with an average detection time of 85 days — a window during which significant damage accumulates.
Call Center Customer Data
High-volume customer data environments such as call centers represent another consistent location for smartphone filming incidents. Agent screens display names, identification numbers, addresses, and contact details in real time. Incidents tend to cluster around employees approaching resignation, or during periods when supervisory coverage is reduced. The data captured in a single session can include hundreds of records.
The Personal Information Protection Commission reported an increase in domestic data breach notifications in 2023, with insider-driven incidents accounting for a substantial portion.

Why Conventional Security Tools Cannot Address This
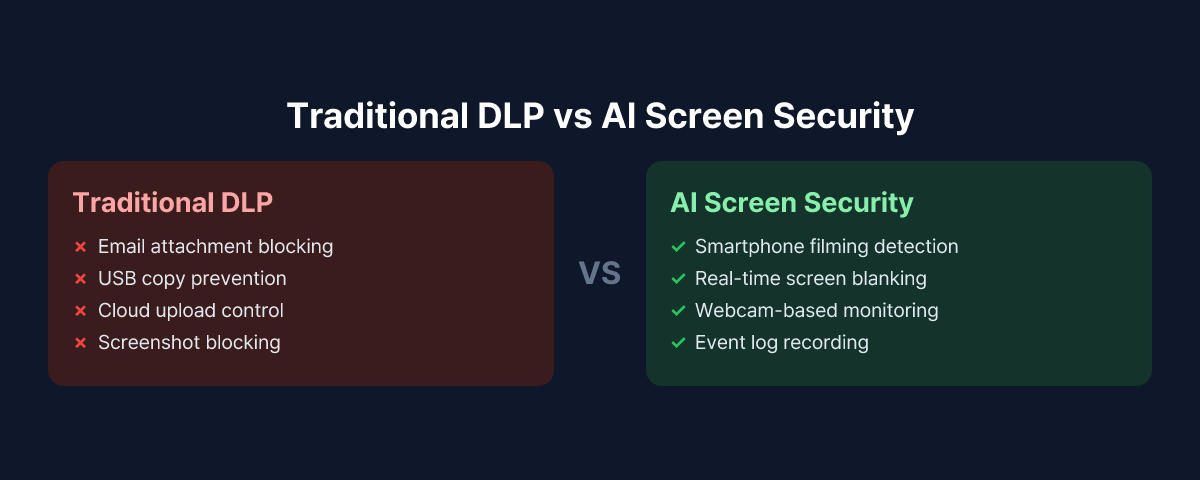
DLP, endpoint security, email gateways, and network monitoring all share a common assumption: that data moves through digital pathways. These tools are designed to intercept data when it is copied, transmitted over a network, or transferred to an external device.
Smartphone photography bypasses this assumption entirely.
When a camera sensor captures the information displayed on a screen, no signal reaches the company's systems. If the employee uses a personal device, it falls completely outside the corporate endpoint agent's scope. Even if the device is connected to the same Wi-Fi network, the act of taking a photograph generates no network activity whatsoever.
As a result, photographing a monitor with a smartphone produces no entry in any conventional security log. This is precisely why it has become a preferred technique in insider threat scenarios — it is effective precisely because it is invisible to existing controls.
Practical Approaches to Preventing Smartphone Filming
Addressing smartphone filming as a threat vector requires more than any single technology or policy. Physical environment controls, documented policy, and technical detection need to work together.
Physical Access Controls
The most direct countermeasure is preventing smartphones from entering areas where sensitive screens are in use. Security-classified zones at financial institutions and government agencies sometimes operate smartphone lockers or enforce camera-disabled device policies. The practical limitation is significant: these measures impose operational friction, are difficult to enforce consistently, and are largely inapplicable in remote work environments or standard office settings.
Policy and Awareness
Organizations should formally document a smartphone photography prohibition as part of screen security policy and ensure employees understand both the rule and the rationale. Establishing policy documentation is also important from a liability standpoint — if an incident occurs in the absence of clear policy, the organization may face a harder time demonstrating that it met its duty of care. Scenario-based training that connects abstract rules to specific consequences tends to be more effective than general compliance messaging.
AI-Based Real-Time Detection
On the technical side, an approach gaining traction is real-time AI detection using the employee's existing PC webcam. The system analyzes the environment around the screen and recognizes when a smartphone is raised toward the display. When that motion is detected, it can trigger an immediate screen blank and send an alert to the security team along with an event record.
MonitorDog implements this capability as part of its screen security platform. The agent running on an employee's workstation uses the webcam to continuously analyze the surrounding environment. When AI detects a smartphone being raised toward the screen, the system blanks the display immediately and logs the event in the administrator dashboard with a timestamp and webcam capture. This approach covers the physical photography blind spot that falls outside conventional DLP's detection range — without requiring new hardware or infrastructure changes beyond installing the agent.
Why Screen Security Deserves Its Own Place in the Security Stack
A common gap in enterprise security thinking is the assumption that DLP covers all data exfiltration pathways. DLP is powerful for digital channels, but it has a structural blind spot for physical methods.
Smartphone filming is the most practical and pervasive form of that blind spot. It requires no technical skill, leaves no trace, operates on a device outside corporate control, and is nearly impossible to detect after the fact without dedicated tooling.
Treating screen security and monitor camera protection as a distinct layer of the security stack — rather than an extension of DLP — may be the piece that current security architectures are missing.
To see how MonitorDog's smartphone filming detection works in a live environment, request a free demo and observe the detection process firsthand.
References
- Financial Supervisory Service, "Financial Company Information Security Survey" (2023)
- Personal Information Protection Commission, "Personal Data Breach Notification Statistics" (2023)
- Ponemon Institute & DTEX Systems, "2024 Cost of Insider Risks Global Report" (2024)
- 3M & Visual Privacy Advisory Council, "Global Visual Hacking Experiment" (2016)