Real Corporate Smartphone Camera Data Breaches and How to Stop Them
In October 2025, police raided LG Display's factory in Paju, Gyeonggi Province. What investigators found on a suspect's phone told the whole story: hundreds of photographs of internal process specifications and engineering designs, taken with a personal smartphone. The company's DLP solution had not triggered a single alert.
3-Line Summary
- Real incidents like the LG Display and Samsung semiconductor leaks show that smartphone photography bypasses every layer of traditional security undetected.
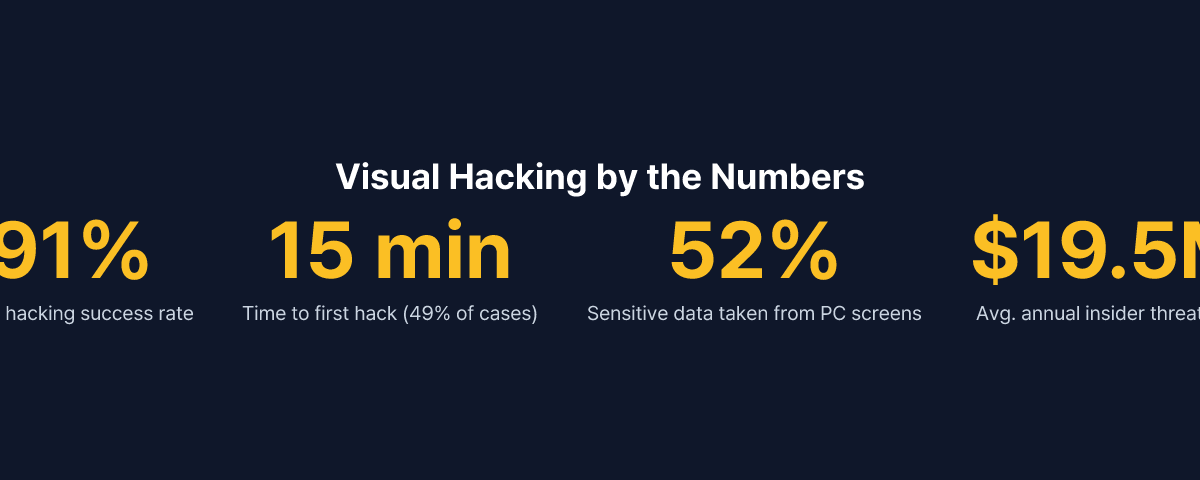
- Visual hacking succeeds in 91% of attempts, and the average annual cost of insider threats per organization now stands at $19.5 million.
- Effective smartphone camera prevention requires three layers working together: physical controls, policy and training, and AI-powered real-time detection.
Smartphone Photography Is Already a Proven Exfiltration Method
The threats that security professionals dismiss as implausible are often the ones most actively exploited. Photographing a monitor screen with a personal smartphone requires no technical skill, leaves no digital trace, and operates entirely outside the reach of every conventional security tool on the market.
A global visual hacking experiment conducted by Ponemon Institute and sponsored by 3M tested this reality across eight countries. The results were stark: 91% of visual hacking attempts succeeded. In 49% of attempts, the first successful hack was completed in under 15 minutes. Of all the sensitive information captured, 52% came directly from employee computer screens.
The implication is straightforward. Walking up to a screen and raising a smartphone is enough to succeed the vast majority of the time — and the security team will never know it happened.
What Actually Happened: Case Studies
Case 1 — LG Display OLED Technology Leak (2024–2025)
In 2024, three former LG Display employees were indicted for leaking core OLED technology to a Chinese company. By October 2025, investigators had expanded the probe to two current employees, executing a search warrant at the Paju factory. On one suspect's phone, police recovered hundreds of photographs of internal technical materials — process specifications and design data that represented some of the company's most sensitive intellectual property.
The method of exfiltration is what matters here. The suspect did not transfer files, send emails, or use a USB drive. The data left the building as photographs on a personal device. No DLP alert fired. No network traffic anomaly was flagged. The company's security infrastructure recorded nothing while the theft was in progress.
Around the same time, Samsung Display's facility in Asan, South Chungcheong Province, was also searched in a separate but structurally identical investigation. The pattern across both incidents points to smartphone photography becoming a normalized exfiltration technique in the semiconductor and display industries.

Case 2 — Samsung Semiconductor Technology Leak
In December 2025, prosecutors indicted ten people, including a former Samsung Electronics executive, for leaking core semiconductor technology to China. Among the methods used: copying critical process information by hand and photographing screens. The court estimated total damages at over five trillion Korean won.
In February 2026, the Supreme Court of Korea remanded the case back to a lower court, holding that acquiring a trade secret and disclosing it must be treated as separate criminal acts. The ruling effectively strengthened the legal basis for treating the act of photographing screens to obtain trade secrets as a standalone offense — even before any external disclosure occurs.
Case 3 — Call Center Personal Data Leaks
In call center environments, smartphone photography is not an isolated incident — it is a recurring pattern. Agents have constant access to customer names, ID numbers, contact information, and financial data displayed on their screens. A single photograph takes seconds, and in densely packed floor environments, real-time supervision by managers is structurally impossible.
According to the Personal Information Protection Commission's 2024 data breach analysis, 307 breach reports were filed in South Korea that year, with internal causes accounting for 30% of all incidents. Because smartphone photography leaves no log, the actual incidence rate is almost certainly higher than reported figures reflect.
Case 4 — R&D Trade Secrets: The Resignation Window
Insider threat research consistently identifies the period between an employee's resignation notice and their last day as the highest-risk window. In documented manufacturing sector cases, departing employees have photographed engineering drawings, process data, and proprietary software interfaces — specifically because they understood that file transfers and USB use would trigger alerts, but a smartphone camera would not.
The 2025 Ponemon Cost of Insider Risks Global Report puts the average annual cost of insider threats at $19.5 million per organization. When incidents are contained within 31 days, the average cost is $10.6 million. When containment takes 91 days or longer, costs rise to $18.7 million. Smartphone photography, precisely because it produces no logs, extends detection and containment timelines — and drives costs upward accordingly.
Why Existing Security Tools Cannot Catch This
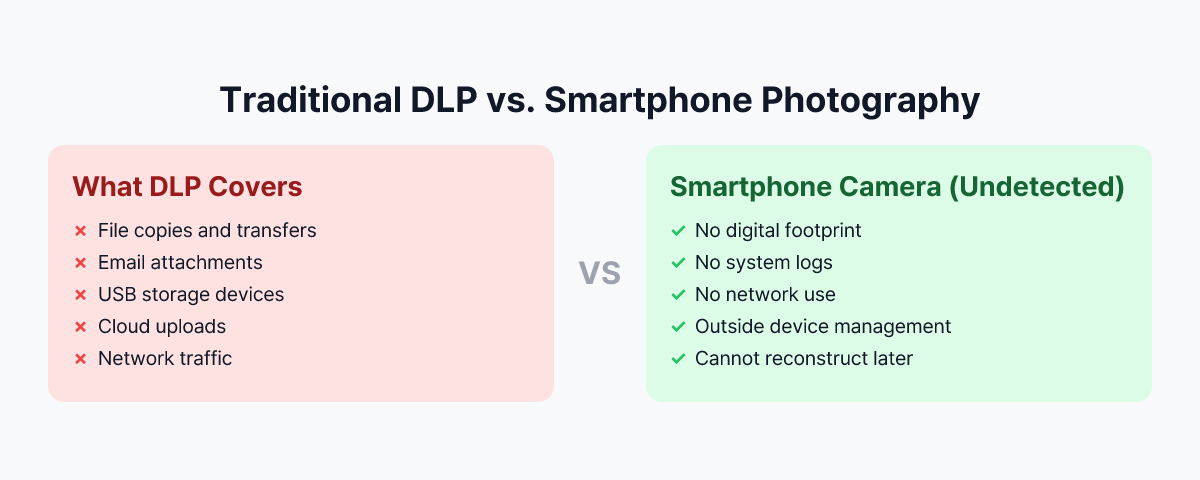
DLP, endpoint security, and network monitoring all share a foundational assumption: that data moves through digital channels. File copies, email attachments, USB connections, cloud uploads — all of these generate system logs that security tools are designed to watch.
Smartphone photography bypasses this assumption entirely. The transfer of information from screen to camera sensor generates no network traffic, no file system events, and no signals that any endpoint agent can intercept. A personal smartphone is outside the company's device management perimeter. Even on the company's own Wi-Fi, the act of taking a photograph uses no network resources.
The LG Display case is a direct demonstration. Hundreds of photographs were taken over an extended period. The company's security systems recorded nothing.
Three Structural Gaps in Current Security Architectures
The first gap is detection scope. Every current DLP solution is engineered to monitor digital channels. Physical channels — specifically the smartphone camera — fall outside the design boundary.
The second gap is device jurisdiction. An employee's personal smartphone cannot have corporate MDM or endpoint agents applied to it. Whatever security posture the company maintains on managed devices does not extend to personal phones.
The third gap is forensic reconstruction. When a file transfer or USB event occurs, the logs survive even if the act itself went unnoticed. Smartphone photography generates no logs at all. When a breach is eventually discovered — often through an external tip or competitive intelligence — the organization cannot reconstruct what was taken, when, or by whom.
A Practical Three-Layer Defense Strategy
Preventing smartphone camera data leaks requires layered controls. No single technology or policy is sufficient. Physical controls, policy and training, and AI-powered detection must operate together.
Layer 1: Physical Environment Controls
The goal of physical controls is to prevent a smartphone from reaching a screen displaying sensitive information.
Phone lockers are a validated approach in financial institutions and government secure facilities. Employees deposit personal devices before entering controlled zones and collect them at exit. The operational overhead is real, but for environments handling the highest-sensitivity data, this remains the most reliable control.
Screen orientation matters. Workstations in areas processing sensitive data should be positioned so that screens do not face corridors, entrances, or visitor paths. The physical separation of visitor traffic from sensitive data processing zones is a baseline requirement.
Privacy filters on monitors reduce exposure from adjacent seats and oblique angles. They do not prevent direct frontal photography, but they reduce the risk of incidental capture and long-distance attempts.
Layer 2: Policy, Training, and Culture
Policy creates the legal foundation for enforcement. Explicit prohibition of photographing work screens must be documented in employee handbooks and security policy documents. A prohibition that exists only as verbal guidance has limited enforceability when an incident occurs.
Training should provide context, not just rules. When employees understand what actually happens when sensitive photographs are taken — including criminal liability under trade secret law — behavioral compliance improves. Specifically: inform employees that photographing screens to obtain trade secrets constitutes a criminal act under Korean law, with exposure to prosecution under the Industrial Technology Protection Act and Criminal Code.
An anonymous reporting channel allows the organization to benefit from peer observation. When colleagues can flag suspicious behavior without personal risk, the organization gains an internal early warning system.
Layer 3: AI-Powered Real-Time Detection
Physical and policy controls have an inherent limitation: they cannot scale to monitor every employee, every screen, every minute. Technology must fill the gap.
MonitorDog uses each employee's PC webcam to run continuous AI analysis of the workspace. When the AI detects a smartphone being raised toward the screen, two responses trigger simultaneously: the screen blanks automatically — hiding the information before it can be photographed — and the security dashboard receives an event notification with a video clip of the moment.
This approach extends security coverage to the physical channel that traditional DLP cannot reach. Deployment requires only an agent installation, with no hardware additions, making it applicable equally to office and remote work environments.
There is also a deterrent effect. When employees know that smartphone photography is detected in real time, the risk calculus changes. The knowledge that the control exists and operates suppresses attempt rates — the system functions as both a detector and a deterrent.
High-Risk Scenarios and Targeted Responses

Applying uniform controls across all contexts reduces operational efficiency without proportional security gains. Focus enhanced controls where risk is highest.
Managing Departing Employees
The resignation-to-last-day window consistently emerges as the highest-risk period in insider threat data. During this window, access privileges should be reduced to the minimum required for remaining duties, and monitoring sensitivity should be increased. In organizations running AI detection systems, lowering alert thresholds for accounts in this window provides additional coverage during the period of elevated risk.
Contractor and Vendor Personnel
Contractors have system access comparable to employees but typically lower organizational loyalty. Access should be scoped tightly to what their work requires, and their presence in areas handling sensitive data should involve escort or direct supervision.
Strategic R&D Zones
Areas where semiconductor designs, new product development, or proprietary algorithms are being worked on warrant stricter smartphone controls than general office spaces. Both the LG Display and Samsung cases involved photography in precisely these environments.
The Legal Dimension: Why Post-Incident Recovery Is Hard
When smartphone photography is the exfiltration method, the legal and operational challenges that follow are compounded by the absence of forensic evidence.
Detection typically comes late — through an external tip, an unexpected shift in a competitor's capabilities, or contact from law enforcement. By the time the organization knows a breach occurred, the window for the 72-hour breach notification requirement under Korea's Personal Information Protection Act has often passed. Organizations face potential penalties for late notification on top of the breach itself.
For trade secret protection, Korean law requires that the company demonstrate it took reasonable steps to maintain confidentiality. An absence of technical controls against physical photography weakens this argument significantly. Conversely, documented AI detection system operation logs, security policy records, and employee training histories serve as evidence that the organization met a reasonable standard of care.
The November 2024 Supreme Court ruling — that trade secret acquisition and disclosure are separate criminal acts — has a practical implication for breach victims as well. It means organizations can potentially pursue criminal liability against a former employee for the act of photographing screens, even if the subsequent disclosure to a third party occurred outside the organization's awareness.
Immediate Checklist: Audit Your Current Posture
The following questions define the minimum baseline for smartphone photography threat coverage.
Does your security policy explicitly prohibit photographing work screens? Verbal-only policies do not create enforceable obligations.
Are sensitive-data workstations positioned so screens do not face corridors, entrances, or visitor areas? If screens are currently visible from public paths, physical rearrangement is the highest-priority quick fix.
Is there a defined process for reducing system access at the point of resignation notice — not just at the last day? The gap between notice and departure is where the risk is highest.
Can any of your current security tools detect smartphone photography? If the answer to this last question is no across your entire security stack, a structural gap exists that DLP, endpoint security, and network monitoring cannot address.
The LG Display case made clear that smartphone photography is not a theoretical risk — it is happening in Korean enterprises today. If you want to see how AI-based detection closes the gap that traditional security tools leave open, MonitorDog's demo will show you the detection process in a real environment.
References
- Electronic Times, "Following Samsung, LG Display Also Shows Signs of Technology Leak to China — Police Execute Search Warrant" (October 2025)
- MBC News, "Three Former LG Display Employees Indicted for Leaking OLED Technology to Chinese Company" (2024)
- YTN, "Prosecutors Indict Former Samsung Executive and Nine Others for Semiconductor Technology Leak" (December 2025)
- Supreme Court of Korea, "Trade Secret Infringement — Prohibition and Damages [Supreme Court ruling, November 14, 2024]"
- Personal Information Protection Commission, "2024 Personal Information Breach Report Analysis" (2025)
- Ponemon Institute & DTEX Systems, "2025 Cost of Insider Risks Global Report" (2025)
- 3M & Ponemon Institute, "Global Visual Hacking Experiment" (2016)
- Verizon, "2025 Data Breach Investigations Report" (2025)